 Image via Wikipedia
Image via WikipediaWhat is a Protocol?
A protocol is simply a rule that defines network communications. In other words, a protocol is a language that computers use to communicate with each other. Just as we humans need to speak and understand the same language to communicate effectively, so do computers. So when I refer to protocols in this article, I am simply referring to a certain type of computer languages.
What are the different types of protocol that exists?
There are many protocols that exist within a network, but I will cover with you a few that I have learned. These protocols will are found within Transmission Control Protocol/ Internet Protocol Suite.
TCP
TCP known as Transmission Control Protocol is a connection oriented protocol. It's main focus is to ensure delivery of data between computers.
HTTP
Hyper Text Transfer Protocol is used by web browsers to transfer files. This protocol is also used to send or transfer web documents between clients and servers.
HTML
Hyper Text Mark Language is known as a data format protocol. This protocol allows for the documents to be read by web browsers. A document needs to have certain tags that act as a translator to allow web browsers to read the documents.
SSL
Secure Socket Layer is a security protocol that insures safe web transaction.
HTTPS
HyperText Transfer Protocol over Secure Socket Layer is a form of security protocol used by web browsers. The url usually begins with HTTPS://. You usually see this type of protocol when you are entering sensitive information over the internet, such as credit card information.
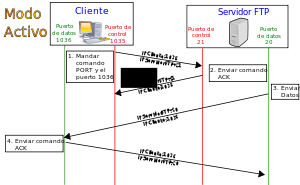
FTP
File Transfer Protocol provides a way to send files. It can transfer binary files. It is a generic method of transferring files. It can include security of files in the form of username and password. FTP url begins with FTP://username&password
SMTP
Simple Mail Transfer Protocol used to send mail to your server.
POP 3
Post Office Protocol 3 is used to download an email from a server to a client. The server holds the email, and the local client can access the email and download it with the help of POP3.
IMAP
Internet Message Access Protocol are settings that is used to get your email. This protocol allows users to access their emails from various locations instead of sending files back and forth between computers. Mail remains on the remote servers and are not actually downloaded to the client system.
TELNET
This protocol is insecure because it data is sent in plain text. Also the device needs to be running the telnet service for it to work. Telnet allows an attached computer to act as a dumb terminal, with data processing taking place on the TCP/IP host computer. It is still widely used to provide connectivity between dissimilar systems. Telnet can also be used to test a service by the use of HTTP commands.
Editors Note: I will update this post as I still do not understand it's main use.
SSH
Secure Shell is the protocol used to protect plain text in TELNET.
DNS
Domain Name Services is a set of rules used to resolve a web name to its numeric address.
Conclusion
These are a few of the protocols that I have learned that is used in Network.
Labsims 701: 6.2.1 Notes - Google Docs: ""
(Via .)

No comments:
Post a Comment